In an increasingly digital world, Windows users have grown accustomed to the security measures that safeguard their systems. Trusted Platform Module (TPM) and Secure Boot are two such features implemented on Windows 11 and later versions designed to protect against unauthorized access and ensure system integrity. However, there may be instances where advanced users or IT professionals find themselves needing more flexibility in customizing their machines. Want to bypass TPM and secure boot on Windows? Our expert guide will show you how, empowering you to customize your system like never before.
Why Bypass TPM and Secure Boot
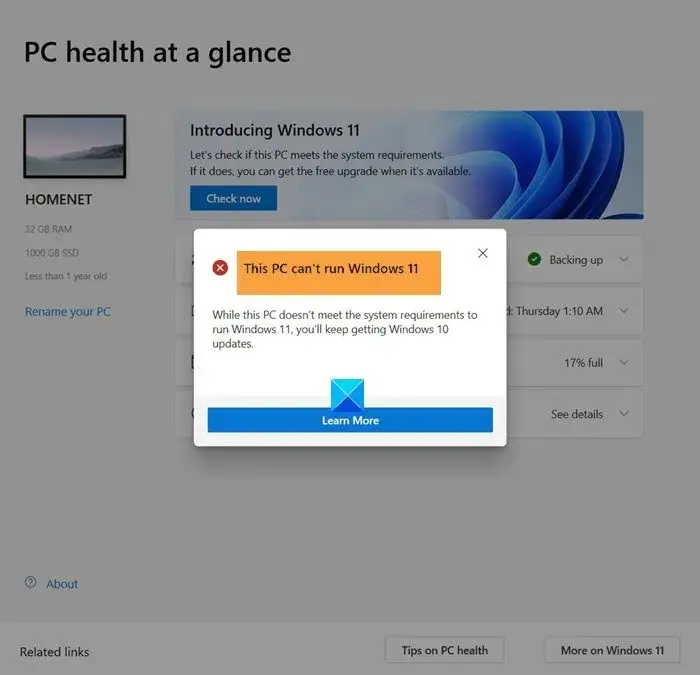
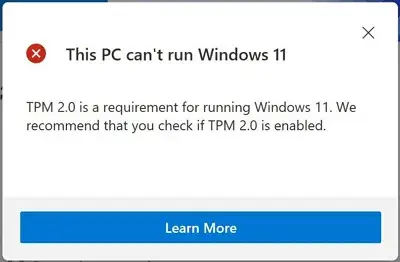
But why would someone want to bypass these seemingly essential security measures? Well, as technology advances, so do the requirements for specific software installations or modifications that may not be compatible with TPM or Secure Boot. For instance, some older hardware components might lack TPM functionalities altogether, limiting users' ability to fully utilize their systems. Additionally, certain customization needs or niche software applications may necessitate a temporary override of these security protocols.
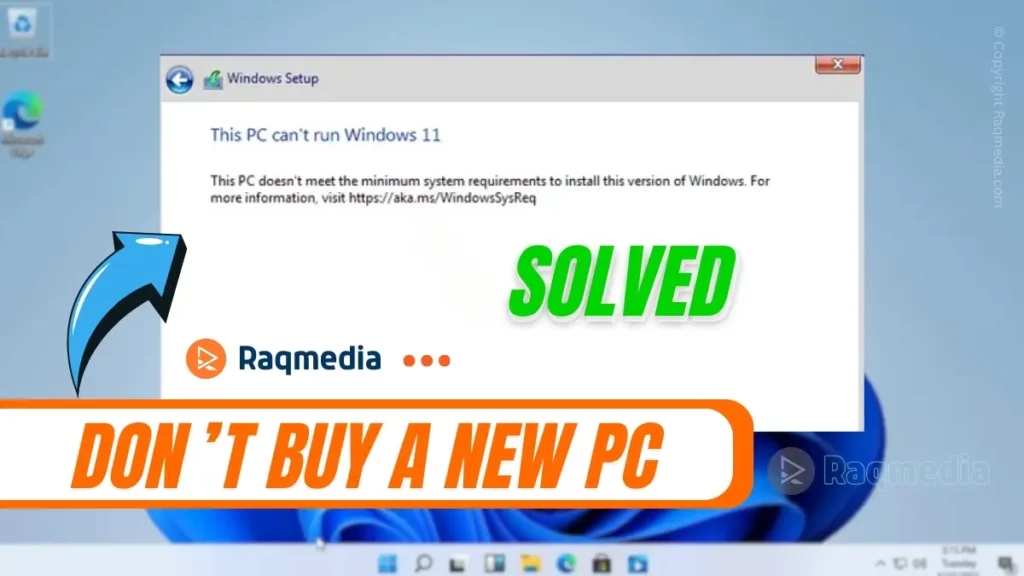
If you're intrigued by the possibilities of modifying your Windows 11 or later machine but find yourself grappling with the constraints imposed by TPM and Secure Boot features—fear not! This comprehensive guide is here to show you how taking control of your system's destiny can be accomplished without compromising its overall well-being.
Join us as we delve into the intricacies of bypassing TPM and Secure Boot on Windows 11 and beyond – unlocking new potentials while understanding the risks involved. In this article, we'll walk you through each step meticulously, providing both technical insight and clear instructions while emphasizing the importance of informed decision-making. Let's create a truly personalized computing experience together!
Understanding Potential Risks
Disabling the Trusted Platform Module (TPM) and Secure Boot on Windows 11 and later versions can grant users more control over their devices, but it also comes with potential risks that should not be taken lightly. One of the primary concerns is the vulnerability of personal data. By bypassing TPM and Secure Boot, users are essentially removing vital security measures designed to protect sensitive information from unauthorized access. This means that if a system is compromised or gets infected with malware, there may be no safeguards in place to prevent data theft or encryption.
Additionally, it's essential to recognize that modifying these security features might have consequences beyond just personal data vulnerability. Disabling TPM and Secure Boot can often void warranty protection on devices as manufacturers typically require adherence to certain security standards for coverage. This means that if any hardware issues arise after disabling these features, repairing them under warranty may become impossible or result in costly out-of-pocket expenses.
How to Bypass TPM And Secure Boot on Windows
Before attempting any modifications to bypass TPM and Secure Boot, users need to carefully evaluate whether the additional flexibility provided by customization outweighs the potential risks associated with compromising system security and losing warranty protection. It is crucial to weigh these considerations thoroughly since once these features are disabled, remedying any negative consequences can prove challenging or even impossible.
By providing a comprehensive understanding of the potential risks involved in disabling TPM and Secure Boot, readers will have a realistic perspective regarding this modification process. Understanding both the benefits gained as well as possible drawbacks ensures individuals make informed decisions when customizing their Windows systems while taking necessary precautions along the way.
Checking System Compatibility
Before attempting to bypass the Trusted Platform Module (TPM) and Secure Boot on Windows 11 and later versions, it is crucial to verify if your device supports disabling these features. Disabling TPM and Secure Boot can have implications for system security and integrity, so it's essential to ensure that your hardware is capable of supporting such modifications.
To check if your device supports disabling TPM, navigate to the BIOS or UEFI firmware settings. This typically involves restarting your computer and pressing a specific key during startup (e.g., Del, F2, Esc) to access the settings menu. Once in the BIOS/UEFI menu, look for options related to TPM configuration or security features. If there is an option labeled Security, Advanced Security, or similar terminology, chances are you will find an option related to TPM within that section.
For verifying support for disabling Secure Boot, follow a similar procedure by accessing the BIOS/UEFI settings menu. Look for options related to boot configuration or boot security settings. Within these settings, you should be able to locate an option regarding Secure Boot enabling/disabling or configuring trusted keys.
Remember that not all devices support disabling these features as they are often integral components of modern computer systems' security architecture. Some manufacturers may even lock down these options entirely on certain models due to compatibility concerns with specific operating systems or potential vulnerabilities associated with leaving them disabled.
Before proceeding further into modifying system configurations that disable TPM and/or Secure Boot on Windows 11 and later versions – ensure you understand any potential consequences like reduced system security against malware attacks using rootkits/hardware-level exploits; restricted access when running certain applications requiring secured environments – ex: virtualization technologies such as Docker/Kubernetes containers where secure platform integrity needs assurance by checking OEM recommendations/documentation online about performing changes under consideration
Disabling TPM Security Features
a. Accessing BIOS settings can vary depending on the device manufacturer and model. For most devices, you will need to restart your computer and press a specific key (such as F2 or Delete) during the startup process to enter BIOS. However, each manufacturer may have a different key or combination of keys to access the BIOS menu. It's important to consult your device's manual or check online resources for the exact key sequence.
b. After accessing the BIOS settings menu, navigate through different screens until you find the section related to TPM security options. The location of this section may differ between manufacturers, but it is often found under tabs like Security, Advanced, or System Configuration. Look for options that mention TPM, such as TPM Device or Trusted Platform Module.
Once you locate these options, there are several actions you can take within the menus:
How to Bypass TPM And Secure Boot on Windows
To disable Secure Boot and gain more control over your Windows operating system, you first need to access the BIOS settings. On Windows 11 and later versions, the process of entering BIOS may vary slightly from previous iterations. Here's a step-by-step guide on how to do it.
1. Start by shutting down your computer completely.
2. Press the power button to turn on your PC, and as soon as you see the manufacturer's logo appear on the screen, press a specific key repeatedly (usually F2 or Delete) to enter BIOS settings. Keep in mind that different manufacturers use different keys for this purpose; therefore, it's important to consult your device documentation or perform an online search if you're unsure about which key to use.
3. Once inside BIOS, navigate through the menus using either arrow keys or mouse (if available). Look for options related to Security, Boot, or UEFI. Again, keep in mind that menu labels might differ depending on your motherboard manufacturer and firmware version.
4. Locate the option labeled Secure Boot within one of these sections. It might be found under various submenus like Security Settings or System Configuration.
5. Disable Secure Boot by selecting its corresponding option and changing it from enabled (On) to disabled (Off). Some systems might require you to set it as custom before allowing complete disabling.
6. Finally, save changes made in the BIOS settings by pressing the designated key shown at the bottom of your screen (usually F10), ensure that all changes are saved when prompted.
By following these steps carefully, you'll successfully disable Secure Boot on your Windows machine and pave the way for further system customization possibilities.
Download The Ready Reg “File Windows 11 Bypass TPM”
Guide: Locating and Disabling Secure Boot Options
To bypass the Secure Boot feature on Windows 11 and later versions, it is essential to locate and disable this option within your device's firmware settings. Please note that the steps may vary slightly depending on the manufacturer and model of your computer. Here's a general guide to help you navigate through this process:
1. Accessing Firmware Settings:
- – Start by shutting down your computer completely.
- – Turn it back on and be ready to press the designated key or combination of keys during startup that will take you to the BIOS/UEFI settings. This key or combination varies among different manufacturers, but common ones include Esc, F2, F10, Del, or Tab.
2. Navigating BIOS/UEFI Settings:
- – Once inside the firmware settings menu, use your keyboard arrows (or specified navigation keys) to move across options.
- – Look for a category related to Security or Boot. It might also be under Advanced Options in some cases.
- – Within these categories, there should be an option called Secure Boot, often accompanied by its status (enabled/disabled).
3. Disabling Secure Boot:
- – Select the Secure Boot option using the appropriate navigation key(s).
- – Toggle its status from Enabled to Disabled.
- – Some systems may require a password confirmation before allowing changes; if prompted, provide your administrator password.
4. Saving Changes:
- – Locate an exit/save button typically placed at either end of the firmware settings menu.
- – Select this button using your keyboard navigation keys.
Remember that disabling Secure Boot can have implications for system security since it allows unauthorized software to run during boot time. Exercise caution when making such modifications and only proceed if you understand and accept any potential risks involved with decreasing overall system security protections.
By following these steps specific to locating and disabling Secure Boot options, you can gain more flexibility when customizing your Windows 11 or later machines. However, it is crucial to exercise discretion and make informed decisions before proceeding further in modifying any security measures on your device.
Post-Disabling Considerations of TPM And Secure Boot on Windows
After successfully bypassing the TPM and Secure Boot on your Windows 11 or later version, it's important to be aware of potential issues that may arise. While enjoying the newfound flexibility in system customization, there are a few considerations to keep in mind.
Firstly, one common issue you may encounter is software installation problems. It's essential to understand that certain applications or drivers rely on the security features provided by TPM and Secure Boot for compatibility and protection. By disabling these features, you might face difficulties installing or running such software. Therefore, before proceeding with any modifications, it's recommended to research thoroughly and ensure that all your desired programs will still function properly without compromising system integrity.
Secondly, it's crucial to maintain vigilance regarding system security after bypassing TPM and Secure Boot. Keep in mind that these security features were implemented for a reason – to safeguard your computer from malicious attacks and unauthorized access. Disabling them increases the risk of potential vulnerabilities being exploited by malware or other threats. Therefore, consider implementing alternative measures such as using reputable antivirus software consistently updating firmware and staying informed about emerging cybersecurity risks.
Lastly, exercise caution when performing future updates or upgrades on your Windows system. Microsoft frequently releases updates designed to improve system stability, fix bugs, enhance performance, and address critical security concerns. However
Risks Of Bypass TPM And Secure Boot on Windows
Before diving into the technical steps of bypassing TPM and Secure Boot on Windows 11 and later versions, it is crucial to emphasize the need for a responsible approach. While the idea of gaining greater control over your system may be enticing, it is essential to consider the potential risks and consequences associated with these modifications.
First and foremost, it's important to note that circumventing TPM and Secure Boot can potentially compromise system security. These features are designed to protect against unauthorized access and ensure the integrity of your operating system. Bypassing them opens up your computer to increased vulnerability, making it more susceptible to malware attacks or other malicious activities.
Furthermore, any changes made during this process may result in instability or compatibility issues with certain software or hardware components. It is possible that bypassing these security measures could lead to unexpected crashes, data loss, or even render your system unusable. Users must understand these implications before proceeding with any modifications.
Therefore, while we provide you with step-by-step instructions on how to bypass TPM and Secure Boot on Windows 11 and later versions, we strongly encourage readers to take utmost caution and thoroughly evaluate whether such modifications align with their specific needs and level of technical expertise. Remember that responsibility lies in understanding the potential risks involved before embarking on any customization journey.
Final Thoughts
In this comprehensive guide, we have explored the process of bypassing TPM and Secure Boot on Windows 11 and later versions. We discussed the technical steps involved in achieving this customization, while also highlighting potential risks that users should be aware of.
It is important to reiterate that these modifications should be approached with caution and responsibility. While gaining more flexibility in system customization can be enticing, it is essential to understand the implications before proceeding. Modifying or bypassing security features like TPM and Secure Boot can leave your system vulnerable to various threats, including malware attacks and unauthorized access.
Therefore, it is crucial for users to weigh the pros and cons carefully before attempting any changes. Ensure you have a thorough understanding of how these security features work and their purpose in protecting your system against potential threats. Research extensively, seek guidance from experts if needed, and always create backups of your data before making any modifications.
Remember: responsible handling of system modifications is key. It's important to strike a balance between personalization and maintaining a secure computing environment. Stay informed about best practices in PC security, keep your operating system updated with patches and security updates provided by Microsoft regularly, use reliable antivirus software, backup regularly – both online or offline –and exercise caution when downloading or installing third-party applications.
By approaching these customizations with care and being mindful of the measures required for system protection along the way ensure you strike that perfect balance between personalization freedom without compromising on overall safety.









🔒 Unlock the secrets to customizing your Windows system with our expert guide on bypassing TPM and Secure Boot! Learn how to gain more flexibility without compromising security.
https://bit.ly/bypsstpm
🖥️ Don’t forget to follow and like for more tech tips!
.
#raqmedia #Windows11 #SecureBoot #TPM #Customization #TechTips #SystemSecurity #WindowsTweaks